
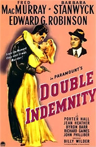
Aggregating anemones (Anthopleura elegantissima). The Aggregating Anemone is the most common species of sea anemone along rocky shorelines on the Pacific coast of North America. It hosts endosymbiotic algae (algae living within its body) called zooxanthellae. The sea anemone benefits from the algae's photosynthesis, receiving oxygen and food as glycerol, glucose and alanine. The algae receive reliable exposure to sun, and protection from micro-feeders.
The anemone is analogous to the supervisor who supports the pet project of a subordinate, while the algae are analogous to the subordinate who nurtures the pet project. In the biological analogy, as in the organizational situation, both parties benefit from the relationship. Photo courtesy U.S. National Park Service.
It isn't surprising when some pet projects get resources — perhaps their nurturers answer to no one, or they abuse their authority. But some pet projects thrive even when their nurturers lack absolute power and seem to have done nothing wrong. Somehow they've found ways to feed their pets without violating organizational policy — or, at least, not much.
In last week's edition, we examined how nurturers of pet projects can abuse their authority to secure resources. Here are some methods that don't necessarily involve abuse of authority, but do depend on cleverness.
- Legitimate circumvention of policy intent
- Sometimes resources flow to pet projects by secretive redirection. In some cases this involves falsification of records, but sometimes the projects' nurturers have exploited flexibility or openings in organizational policy.
- Since even the most primitive control systems involve several people, this technique usually requires collaboration among several individuals, which is difficult to arrange unless the activity is at least superficially legitimate. It's wise to regard these incidents as indicators of (possibly benign) policy defects.
- Exchange of political favors
- In an I-scratch-your-back-you-scratch-mine exchange, two people with access to resources trade those resources, nurturing each other's pets. On the surface, each resource-owner's contribution is legitimate.
- Detecting this tactic is complicated when the exchange crosses supervisory boundaries, because it requires visibility at organizational levels higher than the supervisor of each party to the exchange. It's wise to regard these incidents as indicators of defects in compliance monitoring.
- Scavenging, surplus and mistakes
- Occasionally, possibly as a result of accounting errors, surplus or idle resources become available to anyone who wants them. For instance, some engineering consulting firms have internal R&D programs intended for development of expertise, but these programs can sometimes be deflected to pet projects.
- In many Surplus or idle resources
sometimes become available
to anyone who wants theminstances, the losses to the organization resulting from deflecting these resources are acceptable. Detecting the deflection might not result in much advantage to the organization. But when internal development programs are a means of implementing important strategic decisions, monitoring the use of their resources to inhibit redirection to pet projects can add significant value to the program. - Gifts from above
- At times — usually at the nurturer's request — the nurturer's supervisor might bestow a gift of resources on the pet project, knowing that the organization would not support the project to that extent through routine channels.
- Motivations for such gifts can include a desire to assist the career of the subordinate, and a desire to see the pet project progress. Preventing these gifts might not be advisable, because prevention could conflict with the supervisor's appropriate independence.
By whatever means nurturers secure resources for their pets, they do so in contravention of organizational intent. Fortunately, pet projects do sometimes benefit the organization, and perhaps that's one reason why they're here to stay. First in this series ![]() Top
Top ![]() Next Issue
Next Issue
Is every other day a tense, anxious, angry misery as you watch people around you, who couldn't even think their way through a game of Jacks, win at workplace politics and steal the credit and glory for just about everyone's best work including yours? Read 303 Secrets of Workplace Politics, filled with tips and techniques for succeeding in workplace politics. More info
Your comments are welcome
Would you like to see your comments posted here? rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Workplace Politics:
 Political Framing: Communications
Political Framing: Communications- In organizational politics, one class of toxic tactics is framing — accusing a group or individual
by offering interpretations of their actions to knowingly and falsely make them seem responsible for
reprehensible or negligent acts. Here are some communications tactics framers use.
 I've Got Your Number, Pal
I've Got Your Number, Pal- Recent research has uncovered a human tendency — possibly universal — to believe that we
know others better than others know them, and that we know ourselves better than others know themselves.
These beliefs, rarely acknowledged and often wrong, are at the root of many a toxic conflict of long standing.
 Devious Political Tactics: More from the Field Manual
Devious Political Tactics: More from the Field Manual- Careful observation of workplace politics reveals an assortment of devious tactics that the ruthless
use to gain advantage. Here are some of their techniques, with suggestions for effective responses.
 Passive Deceptions at Work
Passive Deceptions at Work- Among the vast family of workplace deceptions, those that involve camouflage are both the most common
and the most difficult to detect. Here's a look at how passive camouflage can play a role in workplace
deception.
 Virtual Interviews: II
Virtual Interviews: II- The pandemic has made face-to-face job interviews less important. And so we must now also master virtual
interviews, and that requires understanding the effects of the attendance list, video presence, and
the technologies of staging, lighting, and makeup.
See also Workplace Politics and Managing Your Boss for more related articles.
Forthcoming issues of Point Lookout
 Coming April 24: Antipatterns for Time-Constrained Communication: 1
Coming April 24: Antipatterns for Time-Constrained Communication: 1- Knowing how to recognize just a few patterns that can lead to miscommunication can be helpful in reducing the incidence of problems. Here is Part 1 of a collection of communication antipatterns that arise in technical communication under time pressure. Available here and by RSS on April 24.
 And on May 1: Antipatterns for Time-Constrained Communication: 2
And on May 1: Antipatterns for Time-Constrained Communication: 2- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of problems. Here is Part 2 of a collection of antipatterns that arise in technical communication under time pressure, emphasizing those that depend on content. Available here and by RSS on May 1.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!Beware any resource that speaks of "winning" at workplace politics or "defeating" it. You can benefit or not, but there is no score-keeping, and it isn't a game.
- Wikipedia has a nice article with a list of additional resources
- Some public libraries offer collections. Here's an example from Saskatoon.
- Check my own links collection
- LinkedIn's Office Politics discussion group
