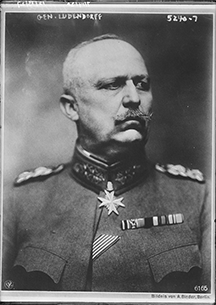
Erich Friedrich Wilhelm Ludendorff (1865-1937) was a German general and politician. He is credited with popularizing the "stab-in-the-back" myth explaining the unbalanced terms of the Treaty of Versailles, a position that led him to affiliate with right-wing politicians and eventually the Nazi Party. See Wheeler-Bennett, John W. "Ludendorff: The Soldier and the Politician," Virginia Quarterly Review 14: pp. 187-202, for an account of the 1919 incident that led Ludendorff to adopt the stab-in-the-back metaphor to make his case to the German people. The nonhyphenated English word, backstabbing, didn't appear until about 1925. Photo courtesy U.S. Library of Congress.
Probably because just about anyone can do it, backstabbing is perhaps the most common form of workplace aggression. The art, of course, lies in executing the aggression undetected. When things haven't gone as well as you expected, almost certainly, once in a while, Chance or Misfortune were not the only cause. A backstabber might have been involved. Let's take a close look at backstabbing — what it is, what it isn't, and how it's done.
The fundamental elements of backstabbing are aggression and deception.
- Aggression
- An interaction can be backstabbing if one person, the attacker, mounts an attack on another, the target. The attack isn't physical, but it must be a genuine attempt to harm the target's social or professional position or prospects, or to deprive the target of something the target desires or needs. The attack can be backstabbing even if it it's unsuccessful.
- Deception
- By concealing preparations, by lying or other disinformation, or by "false flag" conduct, the attacker deceives the target. False flag conduct is that which is intended to create a false belief that the relationship between attacker and target is friendly. Typically, attackers pretend to befriend their targets, or to mentor their targets, or to be disinterested in their targets. By whatever means, the attacker leads the target to believe that no attack is imminent, that the attacker isn't preparing an attack, or that the attacker would never even consider attacking the target.
Some definitions of backstabbing require that the attack occur outside the target's awareness, such as by spreading rumors or lying to third parties in secret. But a direct attack on the target at a meeting, for example, could also be backstabbing if, for instance, the attacker led the target to expect the attacker's support for the target's views in that meeting.
Here are more examples of backstabbing tactics.
- Disclosing confidences
- The attacker By concealing preparations, by
lying or other disinformation,
or by "false flag" conduct, the
attacker deceives the targetpromises to honor a confidence, planning to disclose it later to harm the target. - Withholding helpful information
- The attacker intentionally withholds information from the target so as to cause harm. This tactic is deniable: "I was going to tell you tomorrow," or, "I thought you knew."
- Exaggerating
- The attacker intentionally distorts or exaggerates a report of an event or situation so as to cause harm.
- Lying
- The attacker makes or supports claims that he or she doesn't believe, and which are harmful to the target. See "The Costanza Matrix," Point Lookout for March 16, 2016, for more about lies.
- Stealing or misallocating credit
- The attacker claims credit for the target's contributions, or abets illegitimate claims of others to some of the target's contributions.
- Shifting accountability
- When something goes wrong, the attacker arranges for the target to be held accountable, whether or not the target had any role in the failure.
- Fomenting backstabbing
- The attacker encourages others to engage in any of the tactics above.
When attacked, try to determine whether the attacker used deception. If so, respond with care. Other undetected deceptions might remain active, ready to foil any response you might hastily choose. ![]() Top
Top ![]() Next Issue
Next Issue
Is every other day a tense, anxious, angry misery as you watch people around you, who couldn't even think their way through a game of Jacks, win at workplace politics and steal the credit and glory for just about everyone's best work including yours? Read 303 Secrets of Workplace Politics, filled with tips and techniques for succeeding in workplace politics. More info
Your comments are welcome
Would you like to see your comments posted here? rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Conflict Management:
 Changing the Subject: I
Changing the Subject: I- Whether in small group discussions, large meetings, or chats between friends, changing the subject of
the conversation can be constructive, mischievous, frustrating, creative, tension relieving, necessary,
devious, or outright malicious. What techniques do we use to change the subject, and how can we cope
with them?
 Stonewalling: II
Stonewalling: II- Stonewalling is a tactic of obstruction. Some less sophisticated tactics rely on misrepresentation to
gum up the works. Those that employ bureaucratic methods are more devious. What can you do about stonewalling?
 narcissis
narcissis- When you're responsible for an organizational function, and someone not reporting to you won't recognize
your authority, or doesn't comply with policies you rightfully established, you have a hard time carrying
out your responsibilities. Why does this happen?
 The Myth of Difficult People
The Myth of Difficult People- Many books and Web sites offer advice for dealing with difficult people. There are indeed some difficult
people, but are they as numerous as these books and Web sites would have us believe? I think not.
 Clearing Conflict Fog
Clearing Conflict Fog- At times, groups can become so embroiled in destructive conflict that conventional conflict resolution
becomes ineffective. How does this happen? What can we do about it?
See also Conflict Management and Workplace Politics for more related articles.
Forthcoming issues of Point Lookout
 Coming April 24: Antipatterns for Time-Constrained Communication: 1
Coming April 24: Antipatterns for Time-Constrained Communication: 1- Knowing how to recognize just a few patterns that can lead to miscommunication can be helpful in reducing the incidence of problems. Here is Part 1 of a collection of communication antipatterns that arise in technical communication under time pressure. Available here and by RSS on April 24.
 And on May 1: Antipatterns for Time-Constrained Communication: 2
And on May 1: Antipatterns for Time-Constrained Communication: 2- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of problems. Here is Part 2 of a collection of antipatterns that arise in technical communication under time pressure, emphasizing those that depend on content. Available here and by RSS on May 1.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!