Are you  being bullied at work? Is someone you
supervise bullying you? Do you know how to identify bullying behavior? Do you know what to do
when you experience bullying?
being bullied at work? Is someone you
supervise bullying you? Do you know how to identify bullying behavior? Do you know what to do
when you experience bullying?
Workplace bullying is so widespread that a 2014 survey indicated that that 27% of American workers have experienced bullying firsthand, that 21% have witnessed it, and that 72% are aware that workplace bullying happens. Yet, there are few laws to protect workers from bullies, bullying is not a crime in most jurisdictions, and few employers have specific anti-bullying policies.
101 Tips for Targets of Workplace Bullies is filled with the insights targets of bullying need to find a way to survive, and then to finally end the bullying. It helps you avoid the traps and pitfalls that await you at work, and it guides you into new choices that can right the wrongs you have experienced.
This ebook is also available as an iBook at Apple's iTunes Store. Since all my ebooks are available in Acrobat (PDF) format, you've always been able to read them on ebook readers, such as iPad, iPhone, Nook, or Kindle. But this iTunes version makes use of the special capabilities of modern ebook readers. Check it out!
101 Tips for Targets of Workplace Bullies is a collection of short tips that help targets formulate
effective responses to bullying. You'll learn techniques that cause the bully to find new
targets, and guide the Skip to the Details:
How To Orderorganization towards getting control of its bullies. It gives concrete,
nuts-and-bolts methods for dealing with real-life situations. It's a collection of significant
size — 34 pages (18,000 words) in all.
101 Tips for Targets of Workplace Bullies makes a wonderful and potentially career-saving gift for a friend, a colleague, or a spouse who faces the terror of working while being targeted by a bully.
And it's all packaged in a single, compact ebook. Load it onto your Acrobat-enabled tablet, mobile devices, or laptop and carry it with you on your next trip.
Why I chose to publish this book as an ebook
Ebooks offer the reader several advantages:
- Ebooks are searchable
- If you want to find a passage that uses a particular word or phrase, you can use the search function of your reader to find it very easily. This means I don't have to write an index, which enables me to publish it more rapidly, and to update it more easily. And indices don't always have the words you want anyway.
- You can carry it wherever you carry your reader
- If you use your laptop, tablet, or mobile device as your reader, you can carry your ebook with you without additional weight or space. Great for people who travel, or who find themselves waiting for a meeting to start or for an appointment.
- Ebooks are cheaper than hardcopy
- Many of my ebooks serve a very specialized audience. To provide equivalent content in hardcopy would require unsustainably high pricing.
- Ebooks enable me to address rapidly-varying subject matter
- Change is accelerating. Many of my topic areas are changing so rapidly that the time to publish hardcopy is too long — the content would be obsolete before the book would be available.
The economics of e-publishing enable me to offer you free updates for one year from your purchase date. If a title you purchase is updated within that year, you'll receive an update automatically.
Some sample tips
Here are some sample tips.
- Targets can mount massively coordinated counterattacks
- Counterattacking too feebly is a common error targets make. Bullies know that counterattacks are possible, but since they select "easy" targets, they usually expect feeble counterattacks, if any.
- Bullies generally don't expect massively coordinated counterattacks. That's one reason why massively coordinated counterattacks are so successful. A massively coordinated counterattack is an attack on multiple fronts, simultaneously. Simultaneity overwhelms the bully's ability to process what's happening, enabling the target to get inside the bully's OODA Loop. An example: filing a grievance with your employer, filing a lawsuit against the bully personally, and filing a lawsuit against the employer — all on the same day. The key principle: when you counterattack, escalate to the max. Hold nothing back.
- Coordination with other targets of the same bully or other bullies can be an effective way to overwhelm not only the bullies involved, but also the cognizant officials as they try to suppress any evidence of bullying within the organization.
- Understand how bullies use social isolation
- To isolate someone socially is to deprive her or him of interaction with others. Since humans do need social interaction, this bullying tactic can be very painful for targets. But in most workplaces, complete elimination of social interactions is impossible. That's why bullies focus on the kinds of interaction deprivation that most effectively enhance psychic pain in the target.
- Isolating the target from anyone who might provide support, comfort, or sound advice is the highest priority. Next in priority are techniques that create in the target a sense of being excluded. For example, failing to invite the target to meetings, or having the target attend by telephone rather than in person, could create a sense of exclusion.
- Arranging for the target to work at remote locations facilitates all of these isolation tactics. Supervisors who are bullies sometimes use business travel to isolate targets, especially if the destination is undesirable. But office or cubicle location choices are also useful, if they are remote enough from the target's sources of comfort, support, or advice.
- Bullies who are peers of the target employ social isolation tactics by excluding the target from meetings or informal gatherings with the target's peers. Bullies whose targets are their own supervisors can create a sense of exclusion by organizing meetings or gatherings of the supervisor's subordinates without involving the supervisor.
- Understand the paradox of the "easy target"
- It is widely believed — mistakenly — that bullies always choose "easy targets" — the defenseless and the weak. While it is true that they do find some easy targets attractive, not all attractive targets are "easy targets."
- This circumstance arises because of a paradox. People who are not bullies generally don't appreciate that the difficult targets are precisely those who provide the greatest sense of reward to the bully, because successful bullying of such targets provides the most certain validation of the bully's power. Dominating an easy target proves relatively little.
- That's why bullies don't seek easy targets per se. Rather, bullies prefer targets who provide opportunities for successful outcomes. An individual who is personally strong, but who, for various reasons, is likely to be dominated by the bully, is the most attractive kind of target.
- Be precise when you lodge complaints about bullying
- Imprecision in describing bullying behavior is a common error targets make when they complain to authorities. The imprecision is probably due to our natural inclination to avoid making confrontational statements about each other's behavior when we address each other. That's understandable, and that reluctance is usually a helpful trait, but not so when trying to end bullying.
- For example, a target might approach a Human Resources representative or a supervisor about problems with a bullying peer, saying "I don't know how to talk to her — she almost always misinterprets what I say to mean something malicious, when I don't at all mean anything like that."
- Here the target has made a statement that could reasonably be interpreted to indicate that both the target and the bully need to learn some communications skills, and a recommendation for training might very well be the outcome. The difficulty here is that the target had no such thing in mind, but many supervisors and human resources representatives fail to notice the ambiguity in the wording of the target's complaint.
- What the target could have said was, "I think she is bullying me. She twists almost everything I say — I believe intentionally — so as to make me seem malicious, when I intend no malice, and when I believe no reasonable person could interpret what I said in that way. There is a pattern of bullying here that I believe the organization must address."
- But even that direct approach might not work. A typical response to such a charge is to question the complainant's interpretation of events: "How do you know she misinterprets you intentionally?" You can reply to such skepticism by first restating the question in stronger terms: "An excellent question," you might say. Continuing, "How do I know that the misinterpretation isn't just an accident, and not intentional? I think it highly improbable, because if it were accidental, sometimes she would misinterpret me by making the opposite mistake — by believing that I am too nice, or too supportive. It isn't the misinterpretation alone that leads me to conclude that it is intentional; it is the extreme consistency of the pattern and the consistency in the kind of misinterpretation that leads me to believe that beneath the misinterpretation lies conscious intention. I believe she knows exactly what she's doing."
- Presenting one's case in such stark terms can be very difficult for targets, especially when they have been intimidated by their bullies. But with many supervisors, leaving any opening for a more benign interpretation of one's complaints is likely to result in an unsuccessful outcome.
- Be precise. Say what you mean. If it's too scary, get help and advice in how to approach the problem.
Screenshots
Click one of the miniature screenshot images below to expose a larger image; click that larger image to dismiss it.


The investment
The investment is just — no taxes, no shipping or handling fees. This item requires Adobe Acrobat 6.0 or later or Adobe Acrobat Reader 6.0 or later.
How to order
Make your purchase, and once your order is processed, you'll receive download instructions by return email. To purchase:
This item is also available in a 10-pack (USD 75.00 per pack, or USD 7.50 per copy):
Or as a 50-pack (USD 350.00 per pack, or USD 7.00 per copy):
Or as a 100-pack (USD 575.00 per pack, or USD 5.75 per copy):
Or as a 500-pack (USD 2,375.00 per pack, or USD 4.75 per copy):
This book has an ISBN of 978-1-938932-06-9.
What's in this book
Here's a chapter-by-chapter summary of what you'll find in this tips book.
Click the folder icons to reveal (or hide) individual chapter content summaries, or:
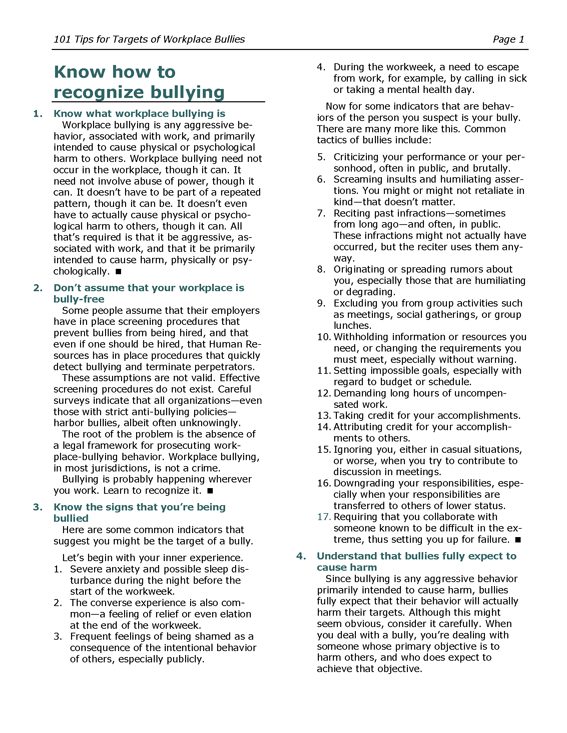
- 1Know what workplace bullying is
- 2Don't assume that your workplace is bully-free
- 3Know the signs that you're being bullied
- 4Understand that bullies fully expect to cause harm
- 5You can decide what bullying is and what it isn't
- 6Bullies do not fit a recognized profile
- 7Know the range of participant roles
- 8Bullies conceive and/or initiate the abuse
- 9The target is the recipient of the bully's abuse
- 10The bully supervisor is the direct supervisor of the bully
- 11Bully assistants carry out the bullying on behalf of the bully
- 12Bully abettors enable the bullying to continue
- 13Bully reinforcers support the bully but don't engage in abuse directly
- 14Silent witnesses observe the bullying but don't acknowledge it
- 15Authorities are managers in the bully's report chain
- 16Target supervisors are usually aware of the bullying
- 17Target allies take the part of the target, sometimes in the moment
- 18Target comforters support the target, usually confidentially
- 19Cognizant officials represent the interests of the organization
- 20The oblivious are unaware of the bullying
- 21Reject the myth that all bullies suffer from low self-esteem
- 22Bullies derive a sense of power from bullying
- 23Bullies interpret inaction by authority figures as endorsement
- 24Others also interpret inaction by authority as endorsement
- 25Bullying is often episodic
- 26Most bullies do not bully out of fear of loss of job
- 27Revenge against the target is rarely a primary motive
- 28Personal animosity towards the target is rarely a primary motive
- 29Conflict is sometimes creative, but bullying is always destructive
- 30In bullying, the bully is always the perpetuator
- 31In bullying, the bully is the initiator
- 32In ordinary toxic conflict, the parties have goals
- 33Denial is common in bullying
- 34In bullying, there is a marked imbalance of power
- 35In bullying there is a stark asymmetry of inner experiences
- 36Set a time limit
- 37Inventory the costs of waiting for relief
- 38Seek personal counseling
- 39Consider couples counseling
- 40Use your vacation days
- 41Targets can feel that they are not in control of their own lives
- 42Targets search for ways to regain control of their lives
- 43Targets often describe themselves as being on a roller coaster
- 44Targets frequently experience social isolation
- 45Many targets feel the urge to flee
- 46Know the possible motivations of the bully supervisor
- 47Know the possible motivations of bully assistants
- 48Know the possible motivations of bully abettors
- 49Know the possible motivations of bully reinforcers
- 50Know the possible motivations of silent witnesses
- 51Know the possible motivations of authorities
- 52Know the possible motivations of the target supervisor
- 53Know the possible motivations of target allies
- 54Know the possible motivations of target comforters
- 55Know the possible motivations of cognizant officials
- 56Know the possible motivations of the oblivious
- 57Know the six strategies of workplace bullying
- 58Understand how bullies use social isolation
- 59Understand how bullies use information manipulation
- 60Understand how bullies use abuse of working conditions
- 61Understand how bullies use emotional abuse
- 62Understand how bullies use professional discrediting
- 63Understand how bullies use professional devaluation
- 64Bullies focus on outcomes
- 65Understand the paradox of the "easy target"
- 66Know the six classes of preferred targets
- 67Know your bully's defensive capabilities
- 68Know how bullies use defensive tactics
- 69Know how bullies use preventative defensive tactics
- 70Bullies aren't necessarily seeking confrontation
- 71Understand the OODA model
- 72Bullies are intuitive users of the OODA model
- 73Bullies use OODA to select targets
- 74Bullies use OODA to control the tempo of the confrontations
- 75Bullies use OODA to shape the bullying environment
- 76Targets are more successful if they accept the necessity of counterattack
- 77Targets should address their own reticence about counterattack
- 78Targets can mount massively coordinated counterattacks
- 79Targets who exploit situational awareness are more successful
- 80Targets can work to degrade the bully's situational awareness
- 81Targets can use deception and disinformation to confuse the bully
- 82Targets must know their own vulnerabilities
- 83Guiding the parties toward achieving common goals doesn't work
- 84Adopting a win-win approach doesn't work
- 85Fostering mutual understanding doesn't work
- 86Encouraging the parties to put the past behind them doesn't work
- 87Encouraging mutual respect, while avoiding talk of punishment and blaming, doesn't work
- 88As a target, avoid revealing your new posture before you're really ready
- 89As a target, know your legal rights
- 90As a target who is the bully's supervisor, combine caution with counterattack
- 91As a target who is the bully's supervisor, plan for the retaliation conversation
- 92Know your employer's anti-bullying policy
- 93Understand why targets wait too long before seeking advice and assistance
- 94Start looking for legal advice long before you think you need it
- 95Find proactive legal representation
- 96Be precise when you lodge complaints about bullying
- 97Be strategic about presenting evidence to authorities
- 98Gathering evidence requires refined observational skills
- 99Commit all your observations to an evidence journal
- 100Understand the value of evidence provided by target allies
- 101Understand the dos and don'ts of audio recording
Follow Rick
Send an email message to a friend
rbrenIyeJIiAfnGdKlUXrner@ChacsxirZwZlENmHUNHioCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!Point Lookout by
starting your Amazon search here

