When we outsource internal processes, we create risk. It's no surprise that the risk created varies with the kind of services outsourced. For instance, outsourcing cubicle maintenance creates risks that differ from those created by outsourcing IT, software testing, or product development. When the risks of outsourcing create threats to the enterprise, we mitigate them — if we fully appreciate the risks.
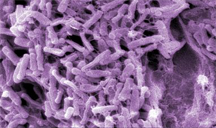
Gut bacteria. The human gut, like the guts of most animals, is populated by hundreds of species of microorganisms. They perform dozens of useful functions for their hosts, many of which are no doubt essential. Without the microbiota, the host species would probably require additional organs to perform these functions. That might be one reason why biologists consider the gut microbiota to be a "virtual organ." In some sense, the host has "outsourced" these functions to the microbiota of the gut. Read more about the gut. Image by Janice Carr, Centers for Disease Control and Prevention, courtesy .
Since some risks associated with outsourcing are inherent to outsourcing, many decision makers haven't encountered them before. Some of these risks are intuitively clear, or have been widely discussed. For example, outsourcing a customer relationship software maintenance task entails some risk of exposure of proprietary information.
But there are other outsourcing risks that are a little less obvious. In the descriptions below, "customer" refers to the organization that decided to outsource some activity, and "vendor" refers to the organization that carries out the outsourced activity.
Part II explores risks associated with the evolution of the processes that are outsourced. In this Part I, I describe risks related to the migration of knowledge to the customers' competitors.
- Knowledge of the outsourcing process
- Knowledge of and experience with the process of outsourcing itself is a customer asset. An example of valuable knowledge: contractual artifacts for managing outsourcing risk. As the customer engages with a vendor, it inevitably transfers that knowledge to the vendor, and from there, the knowledge can migrate to competitors of either party.
- Customers can mitigate this risk by taking care not to reveal intentions during the initial negotiation. Vendors who understand this customer concern can gain trust and loyalty by promising to treat — and then actually treating — contractual terms as if they were the intellectual property of the customer. Often, in effect, they are.
- Improving competitors' processes
- Outsourcing elements Outsourcing elements of internal
processes inevitably transfers
internal knowledge to the vendorof internal processes inevitably transfers internal knowledge to the vendor. When the customer outsources, the vendor necessarily acquires knowledge that previously had been internal to the customer. For instance, the customer might have developed an automated tool for transferring data from one commercial customer relationship management system to another — a tool that isn't available commercially. That knowledge might then propagate to arrangements between the vendor and other customers. Nor is such propagation limited to that one vendor, because its employees carry that knowledge with them when they move to other vendors. - Vendors who accept business only from selected customers who do not compete with each other provide some mitigation of this risk. Customers can mitigate this risk by favoring vendors who don't serve competitors.
The significance of any risk related to outsourcing depends upon the importance of the outsourced process in differentiating the customers' offerings from the offerings of competitors. The more significant a differentiator the outsourced process is, the greater the risk incurred by outsourcing it. Next in this series ![]() Top
Top ![]() Next Issue
Next Issue
Are your projects always (or almost always) late and over budget? Are your project teams plagued by turnover, burnout, and high defect rates? Turn your culture around. Read 52 Tips for Leaders of Project-Oriented Organizations, filled with tips and techniques for organizational leaders. Order Now!
Your comments are welcome
Would you like to see your comments posted here? rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Personal, Team, and Organizational Effectiveness:
 How to Make Meetings Worth Attending
How to Make Meetings Worth Attending- Many of us spend seemingly endless hours in meetings that seem dull, ineffective, or even counterproductive.
Here are some insights to keep in mind that might help make meetings more worthwhile — and maybe
even fun.
 Workplace Myths: Motivating People
Workplace Myths: Motivating People- Up and down the org chart, you can find bits of business wisdom about motivating people. We generally
believe these theories without question. How many of them are true? How many are myths? What are some
of these myths and why do they persist?
 The Good, the Bad, and the Complicated
The Good, the Bad, and the Complicated- In fiction and movies, the world is often simple. There's a protagonist, a goal, and a series of obstacles.
The protagonists and goals are good, and the obstacles are bad. Real life is more complicated.
 A Review of Performance Reviews: Blindsiding
A Review of Performance Reviews: Blindsiding- Ever learn of a complaint about you for the first time at your performance review? If so, you were blindsided.
Reviews can be painful. Here are some guidelines for making them a little fairer.
 High Falutin' Goofy Talk: II
High Falutin' Goofy Talk: II- Speech and writing at work are sometimes little more than high falutin' goofy talk, filled with puff
phrases of unknown meaning and pretentious, tired images. Here's Part II of a collection of phrases
and images to avoid.
See also Personal, Team, and Organizational Effectiveness for more related articles.
Forthcoming issues of Point Lookout
 Coming April 24: Antipatterns for Time-Constrained Communication: 1
Coming April 24: Antipatterns for Time-Constrained Communication: 1- Knowing how to recognize just a few patterns that can lead to miscommunication can be helpful in reducing the incidence of problems. Here is Part 1 of a collection of communication antipatterns that arise in technical communication under time pressure. Available here and by RSS on April 24.
 And on May 1: Antipatterns for Time-Constrained Communication: 2
And on May 1: Antipatterns for Time-Constrained Communication: 2- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of problems. Here is Part 2 of a collection of antipatterns that arise in technical communication under time pressure, emphasizing those that depend on content. Available here and by RSS on May 1.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!