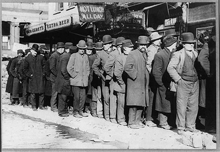
Bowery men waiting for bread in a bread line in New York City in 1910. In some cases, the number of men might exceed the supply of bread, but most of the time, the men did actually receive bread. Those subjected to the whims of Agenda Despots, on the other hand, might well find that their contributions to agendas are never accepted. Meeting attendees who must deal with such a situation rapidly become disenchanted and cynical. Some will decline to contribute to discussions of topics that do appear on the agenda. In this way, the damage done by despotic behavior limits not only what topics are discussed, but also the content of the discussions that do occur. Photo available in the George Grantham Bain Collection of the U.S. Library of Congress.
Although Agenda Despots seek complete control of their meetings' agendas, many organizational cultures value openness and collaborative approaches to meeting management. Many Agenda Despots must therefore feign openness to topics contributed by attendees. Here are seven methods for controlling the agenda without seeming to do so.
- Abuse the not-agenda
- A not-agenda is a list of topics that won't be addressed at the meeting. (See "First Aid for Painful Meetings," Point Lookout for October 24, 2001) Although most meetings don't specify not-agendas, not-agendas can be abused. One method is publishing the not-agenda before soliciting contributions for the agenda, thereby fending off contributions before they're offered.
- Freeze the agenda
- In this approach, Agenda Despots announce a freeze date after which topic contributions can't be considered. By setting this date early enough, or setting it to precede a significant scheduled news-generating event, the Agenda Despot can exclude disfavored topics that depend on late-breaking news.
- Don't solicit agenda contributions
- Some attendees need a little nudge before they dare contribute agenda topics. Some need reminders. By failing to provide nudges or reminders, Agenda Despots attenuate the contributed topic stream, and might even prevent disfavored contributions.
- Abuse the parking lot
- The "parking lot" is a list of topics and issues that arise during the meeting, and which aren't on the agenda. (See "Using the Parking Lot," Point Lookout for September 12, 2007) Parking lot abuse is the systematic ignoring of parked items. They're never addressed. In this way, Agenda Despots can continue to ignore topics that attendees might have contributed for the agenda in advance, and which the Agenda Despot nevertheless excluded from the agenda. If the contributors then raise their excluded topics during the meeting, the Agenda Despot parks them.
- Falsely promise inclusion
- When contributions do arrive, and one of them is unwelcome, the Agenda Despot can claim, "That topic would fit nicely in <name-of-already-included-topic>," which can mollify the contributor. At the meeting, the contributed topic is treated only cursorily, if at all.
- Reject contributions
- Rejecting contributions is always possible,Many of these techniques
are active deceptions but doing so can degrade the Agenda Despot's credibility, especially if he or she has solicited contributions. At times, the price might be worth paying, if the suggested topic is troublesome, and if the Agenda Despot has little credibility left to lose. - Schedule disfavored topics for the end
- When Agenda Despots can't exclude from the agenda a suggested but disfavored topic, they can include it in the agenda, but schedule it near the end of the meeting. When earlier topics overrun their allotted times (if time allotments are published at all), the Agenda Despot, with great (but feigned) regret, can announce that "Regrettably, we must postpone this topic to a later date."
Many of these techniques are active deceptions, because they present the Agenda Despots as being open to contributions when in fact they are not. Using the concept of active deception, see how many additional techniques you can devise. First in this series ![]() Top
Top ![]() Next Issue
Next Issue
Do you spend your days scurrying from meeting to meeting? Do you ever wonder if all these meetings are really necessary? (They aren't) Or whether there isn't some better way to get this work done? (There is) Read 101 Tips for Effective Meetings to learn how to make meetings much more productive and less stressful — and a lot more rare. Order Now!
Your comments are welcome
Would you like to see your comments posted here? rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend me your comments by email, or by Web form.About Point Lookout
 Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
Thank you for reading this article. I hope you enjoyed it and
found it useful, and that you'll consider recommending it to a friend.
This article in its entirety was written by a human being. No machine intelligence was involved in any way.
Point Lookout is a free weekly email newsletter. Browse the archive of past issues. Subscribe for free.
Support Point Lookout by joining the Friends of Point Lookout, as an individual or as an organization.
Do you face a complex interpersonal situation? Send it in, anonymously if you like, and I'll give you my two cents.
Related articles
More articles on Effective Meetings:
 Take Regular Temperature Readings
Take Regular Temperature Readings- Team interactions are unimaginably complex. To avoid misunderstandings, offenses, omissions, and mistaken
suppositions, teams need open communications. But no one has a full picture of everything that's happening.
The Temperature Reading is a tool for surfacing hidden and invisible information, puzzles, appreciations,
frustrations, and feelings.
 When Power Attends the Meeting
When Power Attends the Meeting- When the boss or supervisor of the chair of a regular meeting "sits in," disruption almost
inevitably results, and it's usually invisible to the visitor. Here are some of the risks of sitting
in on the meetings of your subordinates.
 An Agenda for Agendas
An Agenda for Agendas- Most of us believe that the foundation of a well-run meeting is a well-formed agenda. What makes a "well-formed"
agenda? How can we write and manage agendas to make meetings successful?
 Historical Debates at Work
Historical Debates at Work- One obstacle to high performance in teams is the historical debate — arguing about who said what
and when, or who agreed to what and when. Here are suggestions for ending and preventing historical debates.
 Nine Brainstorming Demotivators: I
Nine Brainstorming Demotivators: I- The quality of the output of brainstorming sessions is notoriously variable. One source of variation
is the enthusiasm of contributors. Here's Part I of a set of nine phenomena that can limit contributions
to brainstorm sessions.
See also Effective Meetings and Conflict Management for more related articles.
Forthcoming issues of Point Lookout
 Coming May 1: Antipatterns for Time-Constrained Communication: 2
Coming May 1: Antipatterns for Time-Constrained Communication: 2- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of miscommunications. Here's Part 2 of a collection of antipatterns that arise in communication under time pressure, emphasizing those that depend on content. Available here and by RSS on May 1.
- And on May 8: Antipatterns for Time-Constrained Communication: 3
- Recognizing just a few patterns that can lead to miscommunication can reduce the incidence of problems. Here is Part 3 of a collection of antipatterns that arise in technical communication under time pressure, emphasizing past experiences of participants. Available here and by RSS on May 8.
Coaching services
I offer email and telephone coaching at both corporate and individual rates. Contact Rick for details at rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.com or (650) 787-6475, or toll-free in the continental US at (866) 378-5470.
Get the ebook!
Past issues of Point Lookout are available in six ebooks:
- Get 2001-2 in Geese Don't Land on Twigs (PDF, )
- Get 2003-4 in Why Dogs Wag (PDF, )
- Get 2005-6 in Loopy Things We Do (PDF, )
- Get 2007-8 in Things We Believe That Maybe Aren't So True (PDF, )
- Get 2009-10 in The Questions Not Asked (PDF, )
- Get all of the first twelve years (2001-2012) in The Collected Issues of Point Lookout (PDF, )
Are you a writer, editor or publisher on deadline? Are you looking for an article that will get people talking and get compliments flying your way? You can have 500-1000 words in your inbox in one hour. License any article from this Web site. More info
Follow Rick
Recommend this issue to a friend
Send an email message to a friend
rbrendPtoGuFOkTSMQOzxner@ChacEgGqaylUnkmwIkkwoCanyon.comSend a message to Rick
![]() A Tip A Day feed
A Tip A Day feed
![]() Point Lookout weekly feed
Point Lookout weekly feed
 My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!
My blog, Technical Debt for Policymakers, offers
resources, insights, and conversations of interest to policymakers who are concerned with managing
technical debt within their organizations. Get the millstone of technical debt off the neck of your
organization!